In today’s fast-paced work environment, teams rely heavily on digital tools to chat, share files, and collaborate. Secure internal communication means protecting these everyday exchanges—emails, instant messages, video calls, and documents—within an organization from unauthorized eyes. It ensures that only the intended people can access the information, keeping sensitive details private.
Why does this matter? Businesses handle a lot of confidential data, from client details to financial plans and employee records. A single leak can lead to huge financial losses, legal troubles, damaged reputation, and lost trust among staff. Recent reports show the global average cost of a data breach in 2025 was around $4.44 million, with human error playing a role in most incidents.
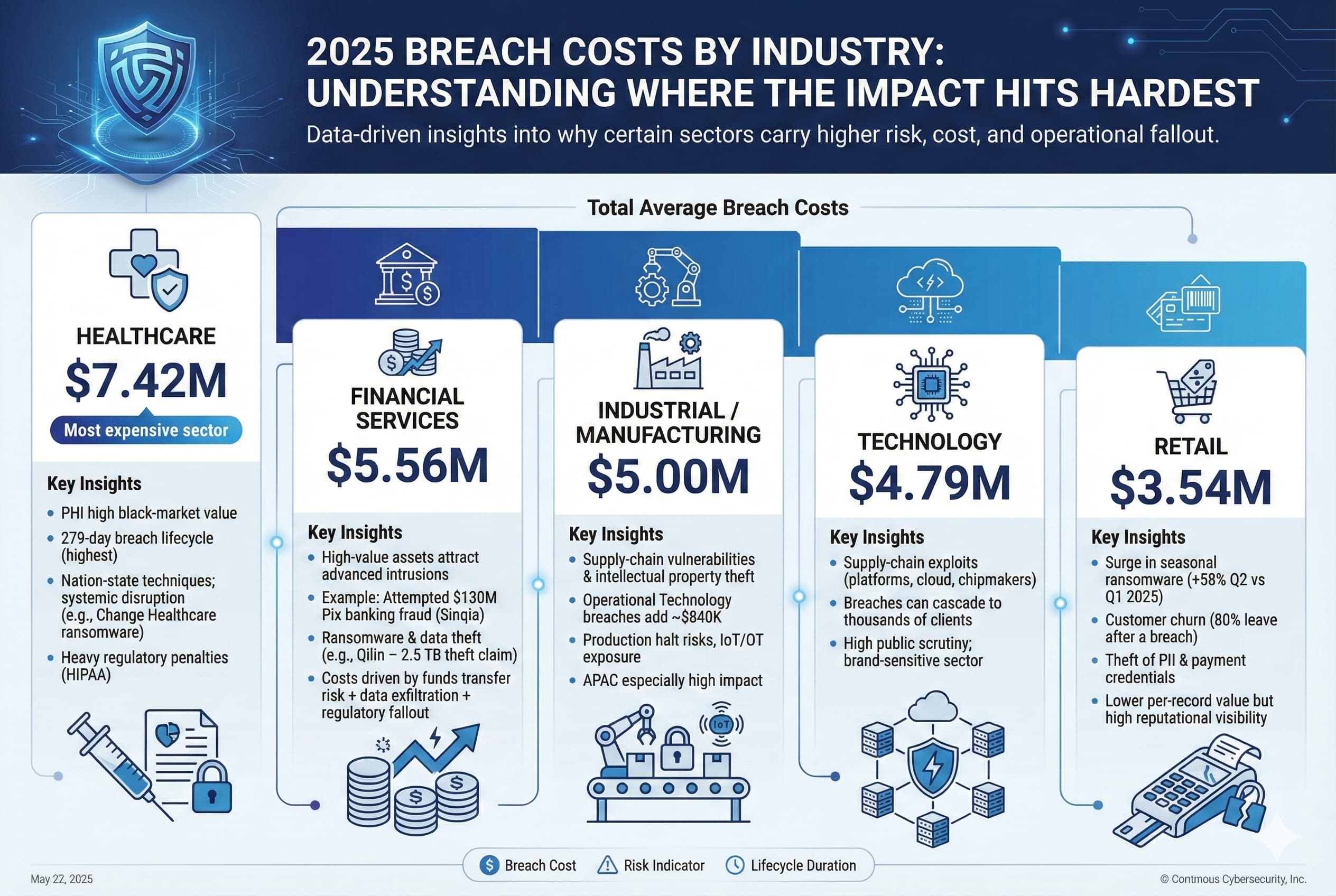
Data Breach Statistics 2025: Global Costs and Trends
With remote and hybrid work still common, communication channels have multiplied, making security more important than ever.
The Risks of Unsecured Internal Communication
Internal conversations often feel private, but they’re a prime target for cyber threats. Here are some common issues:
- Human error: Accidentally sharing sensitive info in the wrong chat or clicking a phishing link. Experts note that mistakes cause the vast majority of breaches.
- Insider threats: Disgruntled employees or careless staff leaking data intentionally or not.
- Shadow IT: Teams using unapproved apps like personal messaging tools, which lack enterprise-level protection.
- Account takeovers: Weak passwords or no multi-factor authentication letting hackers in.
- Metadata leaks and eavesdropping: Even if messages are encrypted, details like who talked to whom can reveal sensitive patterns.
These risks can disrupt operations, lead to regulatory fines (especially under laws like GDPR or HIPAA), and erode team morale.
Latest Insights and Trends
Data from 2025 highlights the ongoing challenge: while breach costs dipped slightly from the previous year, the volume of incidents remained high, with collaboration tools often involved in threats.
Looking ahead to 2026, several trends are emerging from cybersecurity discussions:
- Identity-focused security: Shifting to zero-trust models where every access is verified continuously.
- AI-powered threat detection: Tools that spot unusual behavior in real time, like odd login times or large file transfers.
- Stronger cloud protections: Better encryption and compliance features built into communication platforms.
- Automation for consistency: Automated updates and monitoring to reduce manual errors.
Many online cybersecurity experts emphasize that as deepfakes and AI-generated phishing rise, verifying sources in internal messages will become crucial.
Cybersecurity and Risk Management Best Practices
Practical Solutions and Best Practices
Building secure internal communication doesn’t have to be complicated. Start with these proven steps:
- Choose end-to-end encrypted platforms: Look for tools where messages are scrambled from sender to receiver, with no third-party access—even the provider can’t read them.
- Enforce strong authentication: Require multi-factor authentication (MFA) and single sign-on (SSO) for all logins.
- Set clear access controls: Use role-based permissions so people only see what they need. Separate internal and external channels to avoid mix-ups.
- Train your team regularly: Run simple sessions on spotting phishing, safe sharing, and using approved tools. Make it ongoing, not a one-time thing.
- Create straightforward policies: Define which tools are allowed, how to handle sensitive data, and what to do in case of a suspected issue.
- Secure file sharing and calls: Opt for platforms that encrypt everything—texts, voice, video, and documents.
- Monitor and audit regularly: Review logs, update software promptly, and conduct occasional checks to catch weaknesses early.
Popular options include enterprise versions of Microsoft Teams or Slack (with advanced security add-ons), or more privacy-focused tools like Wire for high-stakes needs. The key is balancing usability with protection so employees actually follow the rules.

Quick Troubleshooting Tips
- If you suspect a breach: Stop sharing, report to IT immediately, and change passwords.
- Employees resisting new tools? Highlight how secure options are often just as easy to use.
- On a budget? Start with free MFA tools and basic training before investing in premium platforms.
Conclusion
Secure internal communication is essential for protecting your organization’s data, complying with laws, and maintaining a trustworthy workplace. By understanding the risks, staying updated on trends like AI detection and zero-trust, and implementing practical steps like encryption and training, you can significantly reduce vulnerabilities.
Start small—audit your current tools and add MFA today. A proactive approach not only prevents costly breaches but also boosts overall team confidence and productivity. In an era where information is power, keeping internal conversations safe is one of the smartest investments you can make.
FAQs
Secure internal communication refers to protecting emails, chats, video calls, and shared files within an organization from unauthorized access or cyber threats.
It helps protect confidential company data, prevents financial loss, maintains legal compliance, and builds trust among employees and clients.
Businesses can reduce insider threats by implementing role-based access controls, monitoring activity logs, and providing regular security training.
MFA adds an extra layer of protection by requiring users to verify their identity through multiple steps before accessing systems.
